My previous blog post addressed the advances in technology and interconnectedness and the benefits and concerns that are associated with this trend. Today we’ll explore the changing landscape of security with a focus on how it impacts various markets and technologies in the physical security space.
The New World of Security by Market
The world of security is undergoing a transformation, driven by technological innovations and evolving threats. As we delve into different markets, it becomes evident that security is no longer a one-dimensional concept. It encompasses an array of facets, ranging from physical to digital, and from personal to national.
Security in Aviation
The safety of passengers, cargo, and airport facilities is paramount. The new world of aviation security is characterized by:
- Advanced screening technologies: Airport security relies on cutting-edge technologies, such as body scanners, explosive detection systems, and passenger biometric authentication.
- Cybersecurity concerns: The aviation industry is increasingly reliant on digital systems, making it vulnerable to cyberattacks. These attacks can range from simple phishing scams to more sophisticated attacks that can compromise critical systems.
- Regulatory Frameworks: Aviation security is influenced by international regulations and agreements, necessitating a harmonized approach to safety and security across borders.
- Physical Security: Airports and airplanes are vulnerable to physical security threats, such as terrorism and hijacking. These threats require a multi-layered approach to security, including screening passengers and luggage, securing the perimeter of airports, and training airline staff to respond to emergencies.
To address these challenges, the aviation industry has looked to other markets—smart buildings and higher security areas—to take advantage of emerging technologies like biometrics and advanced threat detection in order to help keep their facilities safe and secure. These technologies also help with screening the passengers and employees that are occupying these facilities daily. Additionally, airlines and airports are working closely with government agencies to share information and coordinate responses to security threats.
Concerns in Smart Buildings and Cities
Smart buildings and cities are designed to be more efficient and sustainable, but they also present unique security challenges. Smart buildings and cities bring new security considerations, such as:
- Connected Devices: Connected devices, such as smart locks and surveillance cameras, used in smart buildings and cities can be exploited if not adequately protected. Every device is a potential entry point for cybercriminals.
- Data Privacy: Smart buildings and cities collect vast amounts of data about their occupants, which can be used for nefarious purposes if it falls into the wrong hands.
- Physical Security: With the integration of smart technologies, physical security in these environments is not limited to traditional locks and guards. It also involves securing access to digital systems.
To address these challenges, smart building and city operators are investing in new technologies, such as secure communication networks and advanced threat detection systems. Additionally, they need to work with government agencies to develop regulations and standards for cybersecurity and data privacy.
Critical Infrastructure Security
Critical infrastructure, including power plants, water supply networks, and transportation systems, are essential for a society and its economy to function. Protecting critical infrastructure is more challenging due to:
- Increasing Interconnectivity: Critical infrastructure relies heavily on digital control systems, which expose them to cyber threats. A breach in one system can have cascading effects across sectors, which can disrupt essential services and cause widespread damage.
- Resilience Planning: Preparing for physical and digital threats is crucial. Building resilient infrastructure capable of withstanding natural disasters, cyberattacks, and other threats is a priority.
- Public-Private Partnerships: Governments and private sector entities often collaborate to enhance the security of critical infrastructure, emphasizing the need for effective public-private partnerships.
- Physical Security: Critical infrastructure is also vulnerable to physical security threats, such as sabotage and terrorism. Securing critical infrastructure requires a multi-layered approach that includes physical security measures, such as fencing and surveillance cameras, as well as cybersecurity measures to protect against cyber-attacks.
To address these challenges, governments and private companies are investing in new technologies such as advanced threat detection systems and secure communication networks. Additionally, critical infrastructure operators are working closely with government agencies to share information and coordinate responses to security threats.
Implications for other markets
The changing world of security has implications across other markets as well:
- Healthcare: The healthcare industry is digitizing rapidly, necessitating robust data security and compliance with regulations such as the Health Insurance Portability and Accountability Act (HIPAA).
- Financial Services: The finance sector faces constant threats from cyberattacks and fraud, demanding sophisticated security measures to protect assets and data.
- Education: Educational institutions must secure student and staff information and adapt to new security challenges in the age of remote learning.
- E-commerce: The surge in online shopping and payment transactions calls for advanced cybersecurity measures to protect sensitive customer data.
The Technology Side of the New World of Security
Technology plays a pivotal role in addressing these security challenges. Let’s explore how access control, video surveillance, and intrusion detection systems are integral to enhancing security in the new world.
Access Control Systems
Access control systems have evolved significantly with the integration of advanced technologies like biometrics, smart cards, and mobile identity. These systems allow organizations to manage and secure physical access to their premises and data. They have become essential for securing not just traditional office spaces but also data centers, sensitive research facilities, and commercial and residential buildings.
- Biometrics: Facial recognition and fingerprint scanning have become prevalent in access control, offering more secure and convenient identity verification methods.
- Mobile Access: Mobile apps can turn smartphones into secure access identity profiles, allowing users to enter buildings or secure areas with their mobile devices and access systems and spaces around the facility. With the entrance of companies like Apple and Google, the possibilities of how the mobile device can change the user experience (for the better!) is evolving.
- Integration with IoT: Access control systems can be integrated with the Internet of Things (IoT) to provide dynamic access based on real-time data, enhancing security.
Video Surveillance
Video surveillance has seen a massive transformation with enhanced security features that enable real-time monitoring, incident detection, and post-incident analysis.
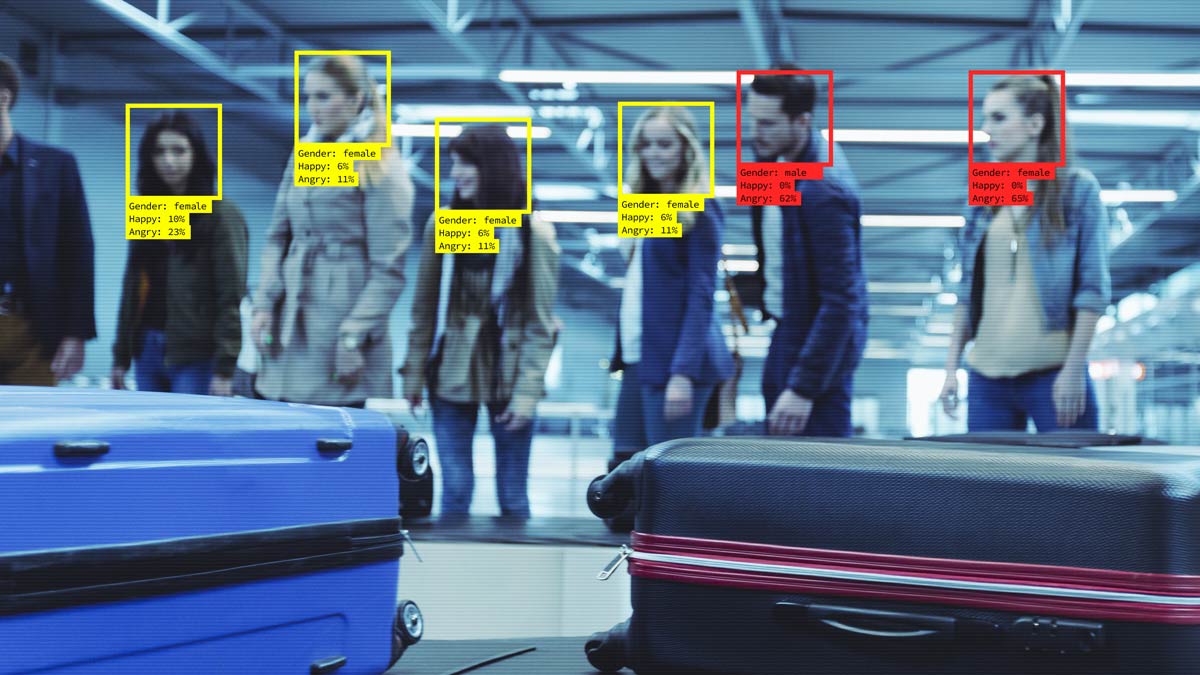
- High-Definition Cameras: High-quality video feeds provide clearer images, making it easier to identify individuals and incidents.
- Cloud Storage: Storing video footage in the cloud offers greater scalability, accessibility, and redundancy for data, reducing the risk of data loss or tampering.
- Video Analytics: Artificial intelligence-powered analytics can automatically detect unusual activities or objects, such as unauthorized access, intruders, or suspicious behavior.
Intrusion Detection Systems (IDS)
Intrusion detection systems are crucial in identifying and mitigating security threats. In the new world, these systems have evolved to detect not only network-based threats but also physical intrusions.
- Network-based IDS: Monitor network traffic for suspicious activities, helping to detect and prevent cyberattacks.
- Host-based IDS: When installed on individual devices, monitor for unauthorized access or system-level anomalies.
- Physical IDS: Sensors, motion detectors, and security cameras detect unauthorized access or intruders.
The convergence of these technologies is also significant. Access control systems can integrate with video surveillance and IDS to provide a holistic security solution. For example, if an unauthorized person gains access to a secure area, the access control system can trigger alarms, lock down the area, and alert security personnel while the video surveillance system records the incident.
The increased connectivity of these system allows for centralized monitoring and control, facilitating security management across multiple locations. However, these interconnected systems generate an unprecedented volume of data about a facility. Beyond analyzing this data, it is imperative to uphold data integrity and privacy while making more informed business decisions.
Conclusion
Security in the new world is intricately linked to the evolution and integration of technologies, such as access control, video surveillance, and intrusion detection systems. These advancements are essential for safeguarding physical spaces and digital assets in an increasingly interconnected and technology-driven society.
To meet the challenges of the new world, stakeholders must adopt a proactive approach that integrates cybersecurity, physical security, and resilience planning.